MCP is fueling agentic AI — and introducing new security risks
Model Context Protocol (MCP) allows AI agents and chatbots to connect to data sources, tools, and other services, but they pose significant risks for enterprises…
How cybersecurity leaders can defend against the spur of AI-driven NHI
Non-human identities were already a challenge for security teams before AI agents came into the picture. Now, companies that haven’t come to grips with this…
AI gives superpowers to BEC attackers
Attackers use business email compromise to pretend to be company executives, vendors, or other trusted parties and trick employees into sending them money. AI makes…
10 things you should include in your AI policy
From understanding what AI means in the context of the organization to being compliant and not forgetting the role third parties play, here are ten…
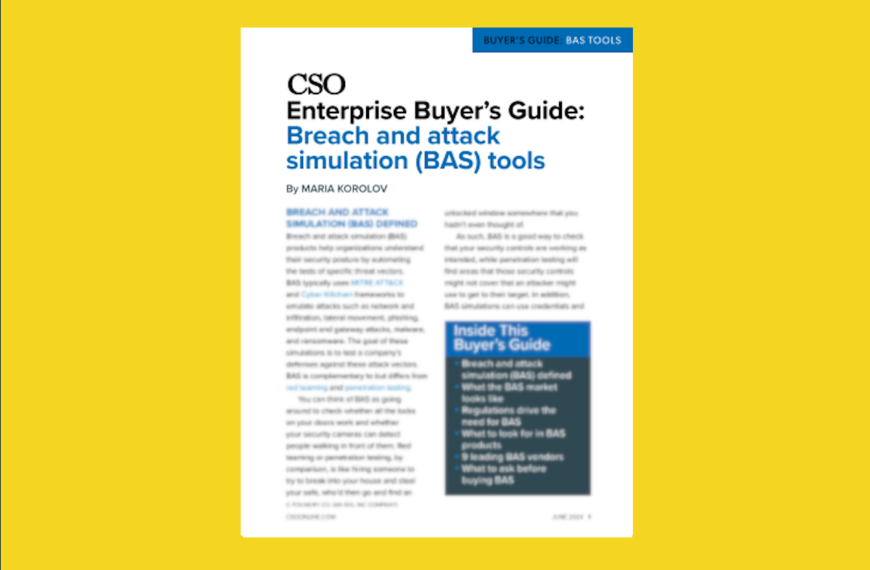
Breach and attack simulation (BAS) tools buyer’s guide
From the editors of CSO, this enterprise buyer’s guide helps IT security staff understand what the various breach and attack simulation (BAS) options can do…
10 most critical LLM vulnerabilities
Prompt injection and supply chain vulnerabilities remain the main LLM vulnerabilities but as the technology evolves new risks come to light including system prompt leakage…
7 ways gen AI can create more work than it saves
As gen AI use continues to skyrocket, reports of business benefits are trickling in. But we’re also seeing more cases where the tech can actually…
10 ways hackers will use machine learning to launch attacks
AI and machine learning are improving cybersecurity, helping human analysts triage threats and close vulnerabilities quicker. But they are also helping threat actors launch bigger,…
10 most critical LLM vulnerabilities
From prompt injections to model theft, OWASP has identified the most prevalent and impactful vulnerabilities found in AI applications based on large language models (LLMs).
Ransomware recovery: 8 steps to successfully restore from backup
The best way to recover from a ransomware attack is to have a reliable and fast backup process. Here’s how to do it.
AI agents can find and exploit known vulnerabilities, study shows
In a somewhat chilling revelation, AI agents were able to find and exploit known vulnerabilities, but only under certain conditions, which researchers say indicates they’re…
Breach and attack simulation tools: Top vendors, key features, how to choose
BAS products simulate attacks to test a company’s defenses against threat vectors. The following guide can help you make the right choice for your organization.
AI governance and cybersecurity certifications: Are they worth it?
Organizations have started to launch AI certifications in governance and cybersecurity but given how immature the space is and how fast it’s changing, are these…
The state of ransomware: Faster, smarter, and meaner
The ransomware business hit record highs in 2023 despite falling payment rates, as attackers scaled up the number of attacks and new AI weapons were…
Generative AI poised to make substantial impact on DevSecOps
Generative AI could be the holy grail of DevSecOps, from writing secure code and documentation to creating tests. But it could be a major point…
How GenAI helps entry-level SOC analysts improve their skills
By automating repetitive triage and documentation tasks, generative AI systems allow entry-level security analysts to spend more time on investigations, response, and developing core skills.
Assessing and quantifying AI risk: A challenge for enterprises
Risks associated with artificial intelligence have grown with the use of GenAI and companies must first understand their risk to create the best protection plan.
3 ways to fix old, unsafe code that lingers from open-source and legacy programs
Code vulnerability is not only a risk of open-source code, with many legacy systems still in use — whether out of necessity or lack of…
Data loss prevention vendors tackle gen AI data risks
Businesses are using DLP tools to help secure generative AI and reduce risks of ChatGPT and similar applications.
5 areas where zero trust can’t protect your organization
With growing adoption of zero trust, CISOs must look at all possible blind spots across the organization, be that unmonitored IoT devices or third-party systems,…
3 strategies that can help stop ransomware before it becomes a crisis
For those hoping to avoid the pay-or-not-to-pay ransomware dilemma, there are three things to focus on that can help CISOs: create incident response plans, improve…
Why API attacks are increasing and how to avoid them
Growing use of APIs give attackers more ways to break authentication controls, exfiltrate data, or perform disruptive acts.
How CISOs can balance the risks and benefits of AI
Rapid growth and development of AI is pushing the limits of cybersecurity and CISOs must take charge now to be ahead of a range of…
Insured companies more likely to be ransomware victims, sometimes more than once
A recent report found that companies with cyber insurance have been hit by ransomware more than those without it, and sometimes more than once. Although…
Siemens focuses on zero trust, legacy hardware, supply chain challenges to ensure cybersecurity of internal systems
Siemens us chief cybersecurity officer Helen Negre discusses how the organization is focusing on zero trust to ensure the security of internal systems across its…
AI-fueled search gives more power to the bad guys
How to stay ahead of attacks by learning about the risks of AI-based search engines, what skill sets are needed to defend systems and ensuring…
How AI chatbot ChatGPT changes the phishing game
The Microsoft-backed free chatbot is improving fast and can not only write emails, essays but can also code. ChatGPT is also polyglot and that could…
The cybersecurity challenges and opportunities of digital twins
The virtual representation of objects or systems through digital twins provide organizations greater insight into their assets but it can also invite malicious actors.
Top 5 security risks of Open RAN
Open RAN enables interoperability among hardware, software, and interfaces used in cellular networks but also changes their attack surface.
6 signs your IAM strategy is failing, and how to fix it
Mistakes when implementing identity and access management systems, especially during upgrades, can have lasting effects. Here’s how to spot and avoid the worst of them.