MCP is fueling agentic AI — and introducing new security risks
Model Context Protocol (MCP) allows AI agents and chatbots to connect to data sources, tools, and other services, but they pose significant risks for enterprises…
Licensing lessons from VMware-Siemens spat
Siemens got into some hot water after Broadcom acquired VMware and changed licensing terms. What can enterprises learn from this dispute?
A timeline of Broadcom/VMware and Siemens licensing dispute
The Broadcom/VMware licensing saga timeline
How cybersecurity leaders can defend against the spur of AI-driven NHI
Non-human identities were already a challenge for security teams before AI agents came into the picture. Now, companies that haven’t come to grips with this…
AI gives superpowers to BEC attackers
Attackers use business email compromise to pretend to be company executives, vendors, or other trusted parties and trick employees into sending them money. AI makes…
Red Hat releases tool to manage edge devices at scale… and to drive cars
The big edge computing news from Red Hat Summit is the first continuously certified Linux OS for vehicles.
Case in point: taking stock of the CrowdStrike outages
It may have faded into obscurity but by an order of magnitude, the outage last July caused by the cybersecurity vendor was the costliest in…
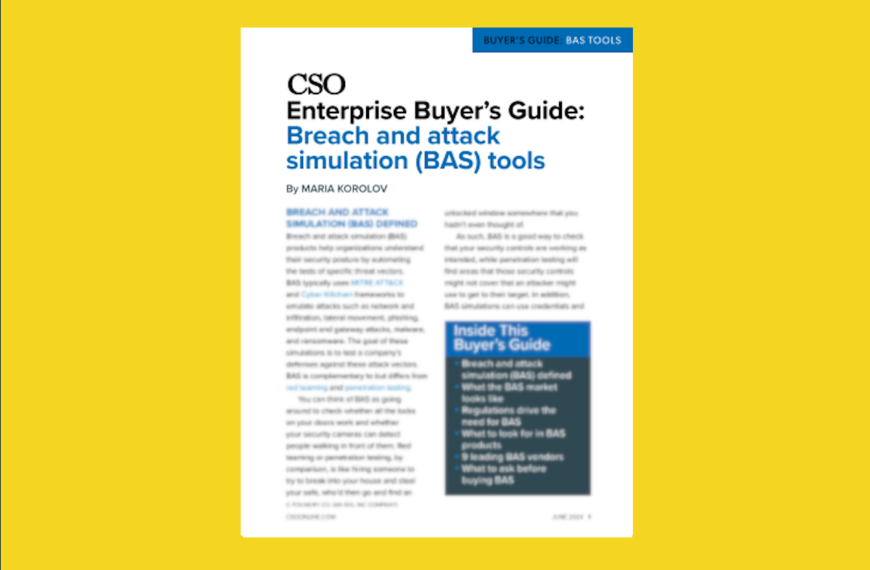
Breach and attack simulation (BAS) tools buyer’s guide
From the editors of CSO, this enterprise buyer’s guide helps IT security staff understand what the various breach and attack simulation (BAS) options can do…
10 most critical LLM vulnerabilities
Prompt injection and supply chain vulnerabilities remain the main LLM vulnerabilities but as the technology evolves new risks come to light including system prompt leakage…
10 ways hackers will use machine learning to launch attacks
AI and machine learning are improving cybersecurity, helping human analysts triage threats and close vulnerabilities quicker. But they are also helping threat actors launch bigger,…
10 most critical LLM vulnerabilities
From prompt injections to model theft, OWASP has identified the most prevalent and impactful vulnerabilities found in AI applications based on large language models (LLMs).
Ransomware recovery: 8 steps to successfully restore from backup
The best way to recover from a ransomware attack is to have a reliable and fast backup process. Here’s how to do it.
NIST finally settles on quantum-safe crypto standards
After years of review, the National Institute of Standards and Technology has chosen three encryption algorithms as the basis for its post-quantum security strategy.
Post-quantum encryption: Crypto flexibility will prepare firms for quantum threat, experts say
NIST standards for quantum-safe encryption are due out this summer. As quantum computing advances, enterprises need to consider their encryption infrastructure and post-quantum security strategies.
Microsoft Entra Suite is late to the SSE pool but will still make waves
Despite being late to market, Microsoft’s secure service edge (SSE) offering has some advantages, including cost and ties to Microsoft’s identity access management services.
AI agents can find and exploit known vulnerabilities, study shows
In a somewhat chilling revelation, AI agents were able to find and exploit known vulnerabilities, but only under certain conditions, which researchers say indicates they’re…
Breach and attack simulation tools: Top vendors, key features, how to choose
BAS products simulate attacks to test a company’s defenses against threat vectors. The following guide can help you make the right choice for your organization.
AI governance and cybersecurity certifications: Are they worth it?
Organizations have started to launch AI certifications in governance and cybersecurity but given how immature the space is and how fast it’s changing, are these…
The state of ransomware: Faster, smarter, and meaner
The ransomware business hit record highs in 2023 despite falling payment rates, as attackers scaled up the number of attacks and new AI weapons were…
Generative AI poised to make substantial impact on DevSecOps
Generative AI could be the holy grail of DevSecOps, from writing secure code and documentation to creating tests. But it could be a major point…
How GenAI helps entry-level SOC analysts improve their skills
By automating repetitive triage and documentation tasks, generative AI systems allow entry-level security analysts to spend more time on investigations, response, and developing core skills.
Assessing and quantifying AI risk: A challenge for enterprises
Risks associated with artificial intelligence have grown with the use of GenAI and companies must first understand their risk to create the best protection plan.
3 ways to fix old, unsafe code that lingers from open-source and legacy programs
Code vulnerability is not only a risk of open-source code, with many legacy systems still in use — whether out of necessity or lack of…
Data loss prevention vendors tackle gen AI data risks
Businesses are using DLP tools to help secure generative AI and reduce risks of ChatGPT and similar applications.
5 areas where zero trust can’t protect your organization
With growing adoption of zero trust, CISOs must look at all possible blind spots across the organization, be that unmonitored IoT devices or third-party systems,…
VMware Cloud gains faster ransomware recovery, expanded management capabilities
Among the announcements at the VMware Explore conference is a new IBM-managed service based on VMware Cloud editions.
VMware NSX+ centralizes cloud networking and security for multicloud environments
VMware NSX+ is a new cloud-managed service that enables consistent network operations and centralized security policy creation and enforcement in multicloud environments.
VMware combines SASE and edge management in new orchestration platform, announces private 5G service
News from the VMware Explore conference includes a unified management platform for VMware’s SASE and edge computing stack, along with a new managed private mobile…
3 strategies that can help stop ransomware before it becomes a crisis
For those hoping to avoid the pay-or-not-to-pay ransomware dilemma, there are three things to focus on that can help CISOs: create incident response plans, improve…
Hybrid mesh firewall platforms gain interest as management challenges intensify
Different types of firewalls, including hardware, virtual, cloud-native, and firewall as a service, can be deployed and managed from a central interface with a hybrid…