Microsoft Entra Suite is late to the SSE pool but will still make waves
General availability of the Microsoft Entra Suite is expected to shake up the nascent SSE industry, putting particular pressure on smaller vendors. SSE – secure service edge…
Proof-of-concept quantum repeaters bring quantum networks a big step closer
Three teams – in Boston, in China, and the Netherlands – have simultaneously announced that they’ve figured out ways to store entangled photons without breaking…
Red Hat seeks to be the platform for enterprise AI
Red Hat went all-in on generative AI at its annual summit last week, offering a wide range of tools for operational and development teams to…
Red Hat unveils image mode for its Linux distro
At the Red Hat Summit this week, the company unveiled a new container image deployment method for Red Hat Enterprise Linux. The new option is…
Red Hat extends Lightspeed generative AI tool to OpenShift and Enterprise Linux
Red Hat’s generative AI-powered Lightspeed tool was first announced last year for the Red Hat Ansible automation platform. This morning, as the Red Hat Summit kicks…
Red Hat introduces ‘policy as code’ for Ansible
Red Hat Ansible’s new “policy as code” capabilities will help users of the infrastructure automation platform to increase efficiency, reduce human error and improve the…
Intel builds world’s largest neuromorphic system
Quantum computing is billed as a transformative computer architecture that’s capable of tackling difficult optimization problems and making AI faster and more efficient. But quantum…
What Microsoft’s error-correction milestone means for usable quantum computing
Microsoft, in collaboration with quantum-computing company Quantinuum, announced that they have reached a new high in quantum error correction, which finally moves the industry into a new…
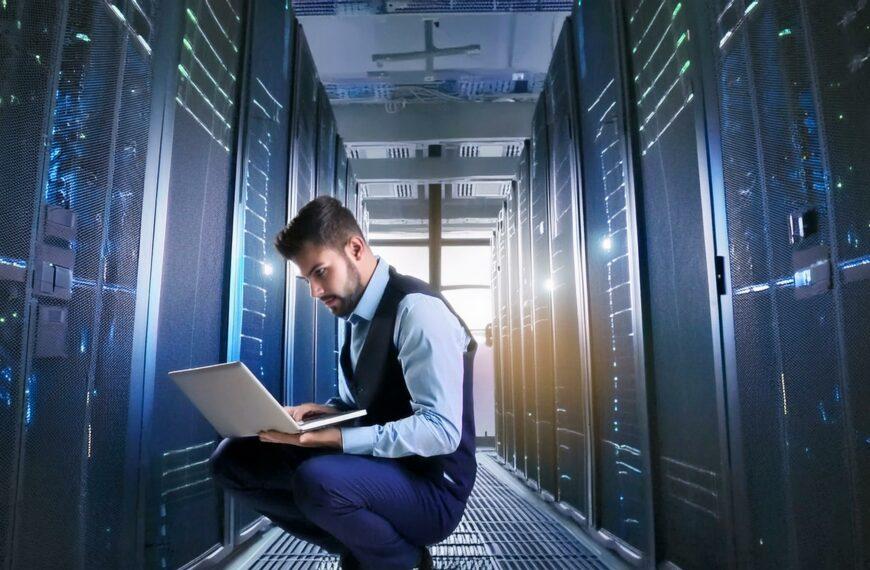
Data centers warm up to liquid cooling
Growing adoption of artificial intelligence and other power-intensive workloads, along with regulatory pressure to reduce energy consumption, is driving a slow but steady transition to liquid…
Error-correction breakthroughs bring quantum computing a step closer
Quantum computing is still in its infancy, easily beaten by traditional computers. One of the biggest challenges? The fact that quantum bits — qubits —…
AI-powered 6G wireless promises big changes
The next evolution in wireless communication, 6G is expected to arrive in 2030, driven by ever-increasing demands for speed and bandwidth from the explosive growth…
5 data center predictions: Surging demand and tighter rules squeeze operations
Five key data center trends will impact operators in the coming year, according to the Uptime Institute. The research firm highlighted the top trends –…
Data centers unprepared for new European energy efficiency regulations
Europe’s new Energy Efficiency Directive goes into effect next May, but the vast majority of data center operators aren’t able to collect the capacity and utilization…
5 ways to boost server efficiency
IT is under greater pressure to address energy efficiency in the data center, particularly as global regulations aimed at sustainability come into play. A key area of…
8 top industries for private 5G
Private 5G networks promise lower latency, higher bandwidth, better security and broader coverage, particularly in challenging environments like mines and factories, compared to more established…
Hot (and not hot) networking skills
Today’s network engineers have to be flexible and adaptable, understand the new infrastructure-as-code paradigm, and stay on top of the latest developments in cloud, security,…
Generative AI dominates VMware Explore news
There were some cloud announcements this week at VMware Explore in Las Vegas, but AI was the star, as it has been at nearly every tech company…
VMware Cloud gains faster ransomware recovery, expanded management capabilities
VMware announced a raft of improvements to its VMware Cloud platform at this week’s VMware Explore conference in Las Vegas. Previously, VMware’s on-premises private cloud…
VMware NSX+ centralizes cloud networking and security for multicloud environments
VMware customers that have both on-prem and cloud-based architecture can now manage networking and security for both in a single management console. Unveiled at this…
VMware combines SASE and edge management in new orchestration platform, announces private 5G service
Combining things to make them easier to manage and secure is a recurring theme at this week’s VMware Explore conference in Las Vegas. To that end, VMware…
VMware, Nvidia team on enterprise-grade AI platform
Companies trying to deploy generative AI today have a major problem. If they use a commercial platform like OpenAI, they have to send data up to the…
Hybrid mesh firewall platforms gain interest as management challenges intensify
As enterprise networks get more complex, so do the firewall deployments. There are on-premises firewalls to manage, along with firewalls that are deployed in virtual…
Flight to cloud drives IaaS networking adoption
As data, applications, and workloads continue to move to the cloud, demand for IaaS networking is surging. The market for cloud-based IaaS networking will reach…
Gartner: SSE landscape shifts as vendors add more security services
The market for managed security services is shifting as enterprises weigh their requirements for cloud-based security capabilities and vendors refine their feature sets and product…
5G network slices could be vulnerable to attack, researchers say
5G promises increased speed, lower latency, and support for a significantly larger number of connected devices. But the growth in devices and in new applications…
Commercial quantum networks inch closer to primetime
As commercial availability of quantum computers moves closer to reality, researchers and vendors are investing in efforts to create quantum-secured networks. Quantum networks use entangled…
Enterprises turn to single-vendor SASE for ease of manageability
Before the start of the Covid epidemic, a traditional WAN architecture with centralized security worked well for Village Roadshow. “Advanced security inspection services can be…
NTT, Palo Alto partner for managed SASE with AIOps
A new offering from IT services provider NTT combines Palo Alto Networks’ Prisma SASE offering with NTT’s managed network services and AIOps infrastructure. SASE – secure…
Pros and cons of managed SASE
AmerCareRoyal, which provides disposable products for the food service and hospitality industries, is the product of six mergers and acquisitions over the past several years,…
What to expect from SASE certifications
Secure access service edge (SASE) is a network architecture that rolls SD-WAN and security into a single, centrally-managed cloud service that promises simplified WAN deployment,…