Latest Stories
Keeping humans in the AI loop
The standard advice for guaranteeing AI safety and accuracy is ensuring human oversight. But even humans have their limits, especially as companies scale up AI deployments.
-
/
Keeping humans in the AI loop
-
/
What CIOs need to know about measuring AI value
-
/
How cybersecurity leaders are securing AI infrastructures
-
AI will drive more workforce expansion for tech pros than reduction, Linux Foundation reports
-
I vibe-coded a dog birthday app. We still need developers.
-
/
Top 10 MCP vulnerabilities: The hidden risks of AI integrations
Award-winning articles
-

Broadcom’s vision for VMware highlights private clouds, private AI
-

With Project Cypress, VMware brings generative AI to cyberdefense
-

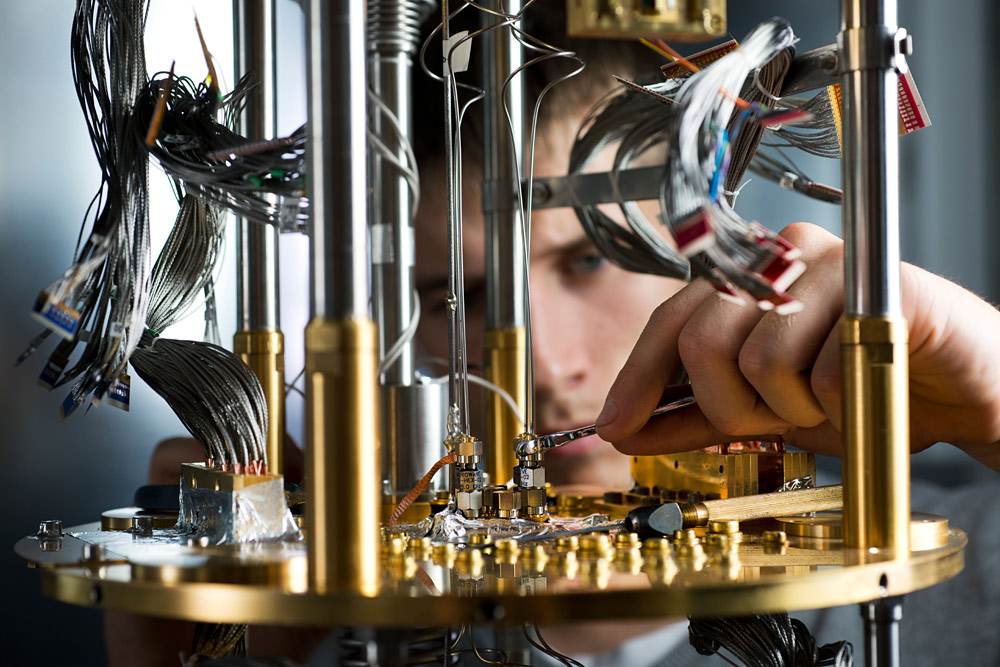
NIST finally settles on quantum-safe crypto standards
-

Post-quantum encryption: Crypto flexibility will prepare firms for quantum threat, experts say
-
Proof-of-concept quantum repeaters bring quantum networks a big step closer
-

Error-correction breakthroughs bring quantum computing a step closer
-

How AI chatbot ChatGPT changes the phishing game
-

Private 5G keeps Whirlpool driverless vehicles rolling
Artificial Intelligence
-
/
What CIOs need to know about measuring AI value
Even though many companies report positive ROI from gen AI, IT leaders don’t always know how to actually measure it, and the vast majority of AI projects fail. So what’s the real story, and what metrics are important to gauge AI success?
-
/
How cybersecurity leaders are securing AI infrastructures
AI models, agentic frameworks, data pipelines, and all the tools, services, and open-source libraries that make AI possible are evolving quickly and cybersecurity leaders must be on top of it.
-
AI will drive more workforce expansion for tech pros than reduction, Linux Foundation reports
The big takeaway from this year’s Linux Foundation tech talent report is that despite fears of layoffs, jobs are being created, with particular growth in jobs requiring AI. In addition, there are still significant talent shortages in cybersecurity, cloud, and platform engineering.
-
I vibe-coded a dog birthday app. We still need developers.
Can a non-developer use vibe coding to build and deploy a full-stack app? And can that app actually do anything useful?
-
/
MCP is fueling agentic AI — and introducing new security risks
Model Context Protocol (MCP) allows AI agents and chatbots to connect to data sources, tools, and other services, but they pose significant risks for enterprises that roll them out without having proper security guardrails in place.
-
/
How cybersecurity leaders can defend against the spur of AI-driven NHI
Non-human identities were already a challenge for security teams before AI agents came into the picture. Now, companies that haven’t come to grips with this problem will see it become even more critical.
-
/
Top 9 generative AI use cases for business
Advanced chatbots, digital assistants, and coding helpers seem to be some of the sweet spots for gen AI use so far in business.
spotlight
About
Maria Korolov is an award-winning technology journalist who covers artificial intelligence, cybersecurity, and quantum computing.

CONTACT
The best way to reach Maria Korolov is by email at [email protected].
Latest Quantum Computing Articles
IBM announced an error correction breakthrough that will lead to a large-scale, fault-tolerant quantum computer by 2029.
Errors are the top obstacle preventing the industry from having usable quantum computers.
The time is now to create cryptography polices and plan for a transition to post-quantum encryption.
The Defense Advanced Research Projects Agency has selected 15 quantum computing companies to help bring quantum computing closer, and is spending millions on the project.
IonQ and Alice & Bob, have both announced breakthroughs that bring quantum computing closer to reality
D-Wave explains how quantum supremacy can be used to handle more than theoretical problems
Latest Cybersecurity Articles
Broadcom adds agentic security, post-quantum encryption, and other features to VMware Cloud Foundation, vDefend and VMware Avi Load Balancer.
AI models, agentic frameworks, data pipelines, and all the tools, services, and open-source libraries that make AI possible are evolving quickly and cybersecurity leaders must be on top of it.
Model Context Protocol (MCP) use is increasing in popularity for connecting AI agents to data sources, and other services. But so too are vulnerabilities that bring unique risks to agentic systems.
Model Context Protocol (MCP) allows AI agents and chatbots to connect to data sources, tools, and other services, but they pose significant risks for enterprises that roll them out without having proper security guardrails in place.
Siemens got into some hot water after Broadcom acquired VMware and changed licensing terms. What can enterprises learn from this dispute?
The Broadcom/VMware licensing saga timeline
Latest Blog Posts
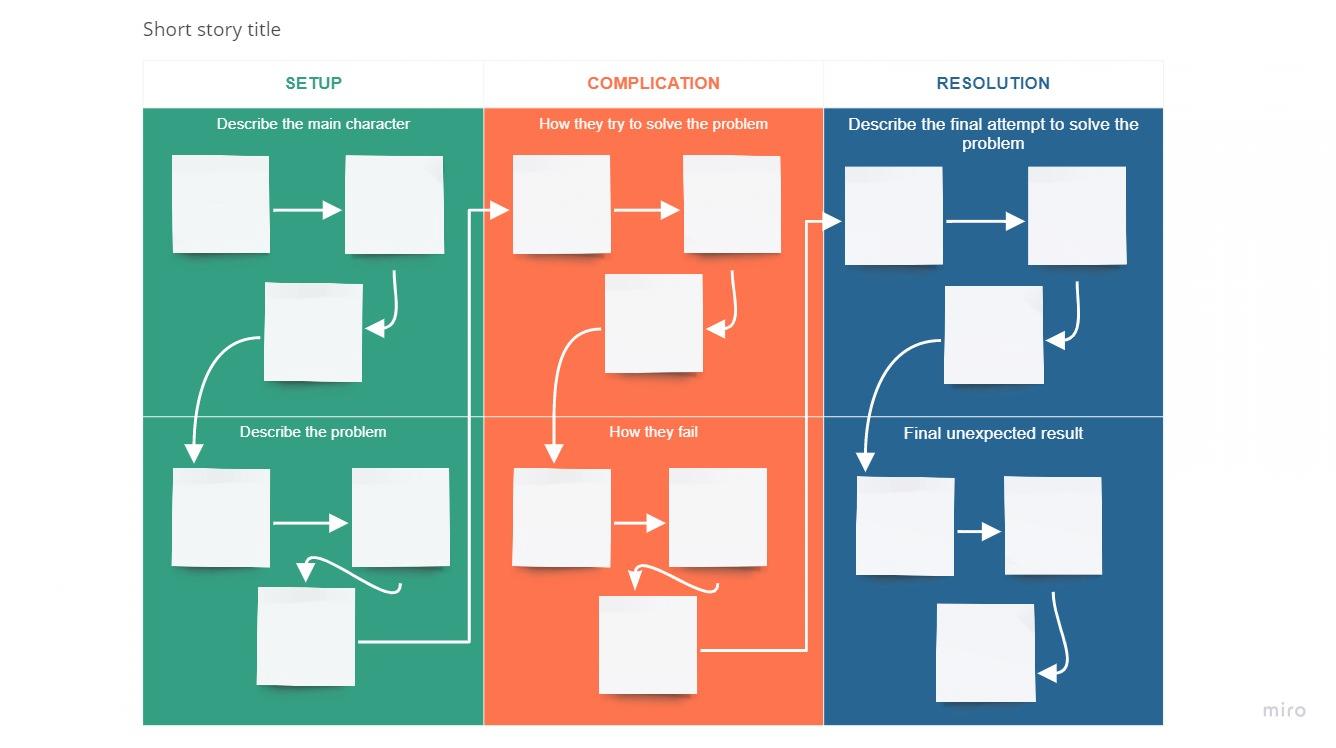
How the use the free Miro app to outline your story or novel.
Here are seven books on Amazon with over a 100 positive reviews that will help you finish your writing project — are free to read…
Have you ever stared at your screen or typewriter or notebook and couldn’t force yourself to write? I have, and here’s what I do to…
Pre-made book cover sites offer low-cost, professional-looking covers for independent authors.
“Show, don’t tell” is the first lesson of Fiction Writing 101, and one of the easiest and quickest fixes is to replace the emotional adverbs…
Our master list of best resources for writers of fantasy, horror and sci-fi. Writing advice sites Writer’s Knowledge Base: Huge database of more than 40,000…